Stealth hypervisor-based analyzer
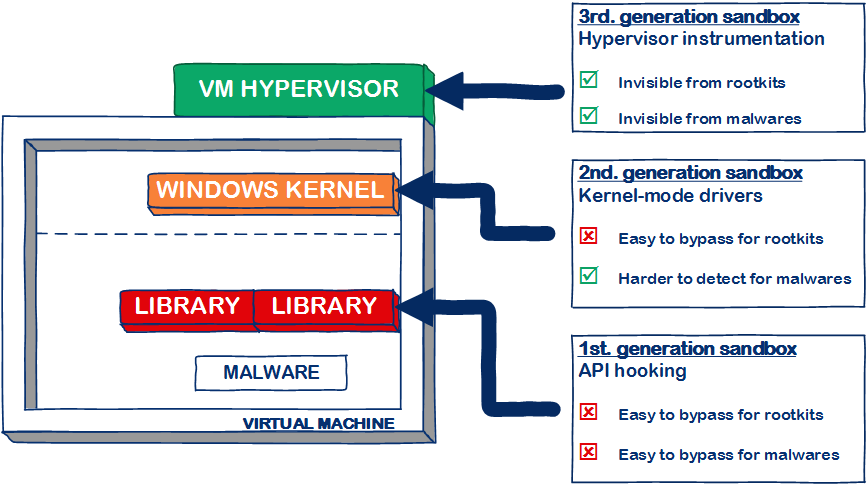
Most sandboxing solutions rely on an agent component installed inside the virtual environment. Nowadays, malware actively try to detect sandbox softwares, and these agents are easy targets. Evasion technique like hook detection or driver listing have been used for several years against well-known sandbox softwares.
The P2A sandbox is a third generation sandbox featuring a state-of-the-art hypervisor introspection technology. By moving the analysis component outside of the virtual machine, our technology drastically diminishes the surface for sandbox detection attacks. If you add to this an extensive list of anti-anti-VM and anti-anti-analysis tricks implemented by our best analysts, you obtain a sandbox that is both harder to detect and harder to evade than first and second generation sandboxes. It is able to bypass all pafish benchmarks for instance.
More InfoFirst generation sandboxing
The first generation sandbox solutions, which include Cuckoo sandbox, are based on the API hooking technology. A sandbox agent, located inside the virtual machine, will inject a piece of code (most of the time a DLL) inside monitored processes running in the VM. The injected code will modify system DLLs in order to intercept and analyze Windows library calls.
While easy to develop, this technology is also the easiest to detect. Detection of first generation hooking can be achieved through the following means:
- By scanning its own process memory and looking for injected code, a malware is able to detect the sandboxed environment
- By verifying system DLL function prologues, a malware is easily able to detect the presence of API hooks
- By looking for the presence of the agent in the system, or any artifact of said agent, a malware is able to detect the presence of a specific sandbox solution
There are also many way to evade first generation sandboxing:
- By using low-level system calls (int 2e/syscall/sysenter), advanced malware is able to completely bypass first generation monitoring. The Kronos malware for instance makes heavy use of this technique.
- Hooking can also be bypassed by calling the on-disk version of system DLLs, instead of the in-memory DLLs that have been hooked by the sandbox.
- Since the sandbox agent is located inside the virtual machine, it has to send the analysis data to the host at some point. A malware could also attack this weak point by deleting agent files, shutting down network connection or rebooting the computer. Without analysis data, no useful report would be shown for such malware.
Second generation sandboxing
Second generation sandbox solutions, such as Hybrid Analysis / Vx streams, tried to overcome some of the aforementioned drawbacks while staying relatively easy to maintain. Those newer solutions are based on a custom Windows kernel driver deployed inside the virtual machine, which is in charge of the analysis. While this is theoretically equivalent to the first-generation agent (the driver is inside the VM), it offer two technical advantages over the older solution:
- By using rootkit-like techniques, it is easier for second-generation sandboxing to hide the kernel-driver agent from user-mode malware
- Since the agent is located inside the Windows kernel, it is able to intercept the Windows system calls at a lower level, leveraging the need for DLL hooking
Second generation sandboxes have a smaller attack surface, but can be detected nonetheless by determined attackers:
- While it is a lot harder for malware to detect the presence of the sandboxing kernel driver (especially if it actively hides its present), it is not impossible. By loading malicious driver, a malware may gain access to the Windows kernel and thus detect the sandbox driver agent.
- Timing attacks are another mean of detecting this kind of monitoring. The additional time spent inside the monitoring kernel driver can be measured by the malware and compared with reference benchmarks. This technique is prone to false positives tho.
There are also ways to evade second generation kernel monitoring:
- Malicious kernel driver may attempt to remove the monitoring kernel driver.
- Deleting agent files, shutting down network connection or rebooting the computer may also interfere with the transmission of the analysis results.
High performance solution
The P2A analyzer is based on the industry-recognized KVM hypervisor. By making heavy use of the VMx CPU extensions for VM introspection, the P2A sandbox is able to run malware at near native speeds. If add the possibility to create large clusters of analysis machines, you obtain a sandboxing solution that is able to handle several hundred thousands of samples per day for a limited hardware investment.
Additionally, the P2A sandbox embeds several counter-measures against the class of malware that actively try to delay their execution in order to evade detection.
- Our analyzer is able to selectively alter time-measurement functions inside the monitored processes. By maintaining a virtual time that flows several times faster than the system clock, the P2A is able to force latent malicious code to execute.
- Scheduled tasks that are registered by the malware inside the VM are also handled and triggered immediately.
- The P2A framework is able to resist API-hammering techniques, a technique aimed at slowing down the monitoring component of traditional sandbox solutions.
All these features combined allows us to deliver high quality reports, showing a lot of the malware potent activity, in a limited amount of time. A typical P2A analysis is done in 1 or 2 minutes, whereas most of our competitors need 3 to 10 minutes per sample in order to show interesting malicious behavior.